
Hacking Articles on X: "Linux privilege Escalation Credit @xtremepentest #infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #linux #cybersecurityawareness ...
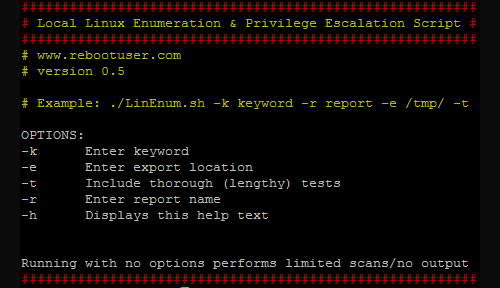
LinEnum - Linux Enumeration & Privilege Escalation Tool - Darknet - Hacking Tools, Hacker News & Cyber Security

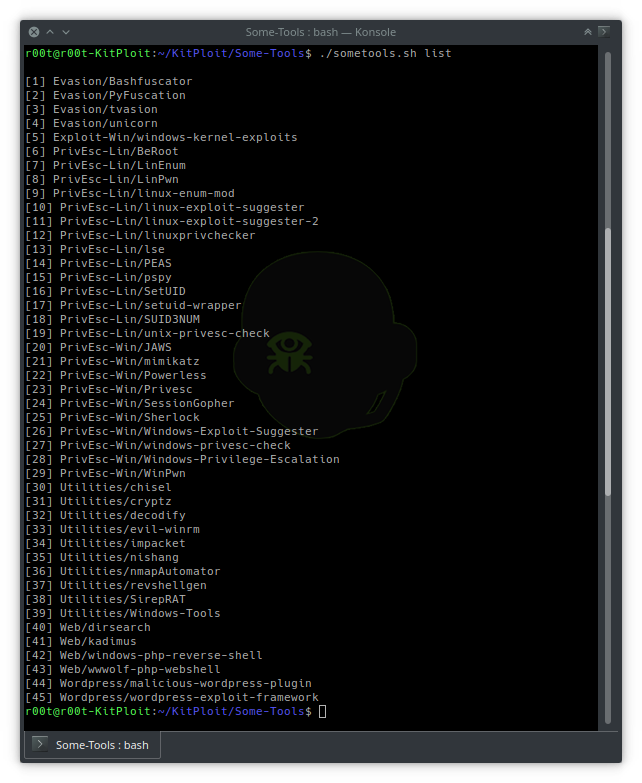
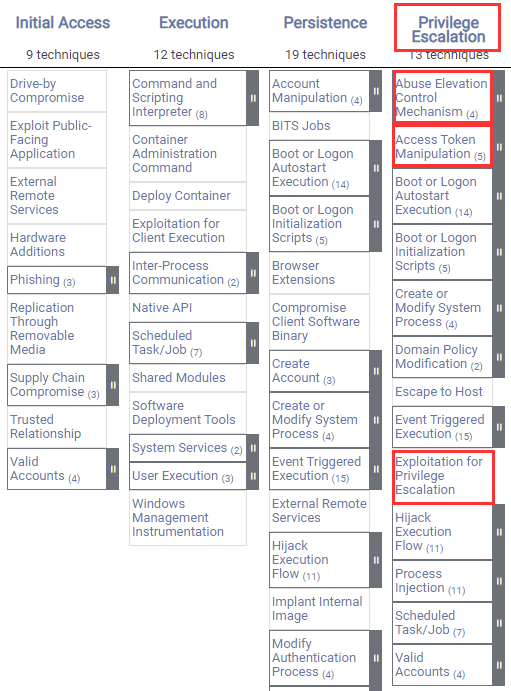
Offensive Security Tool: PEASS (Privilege Escalation Awesome Scripts Suite) As Shell is the beginning, once a hacker accesses a system, which is not so... | By Black Hat Ethical HackingFacebook

Hacking Articles on X: "Privilege Escalation Tools #infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #linux #cybersecurityawareness #bugbounty #bugbountytips ...
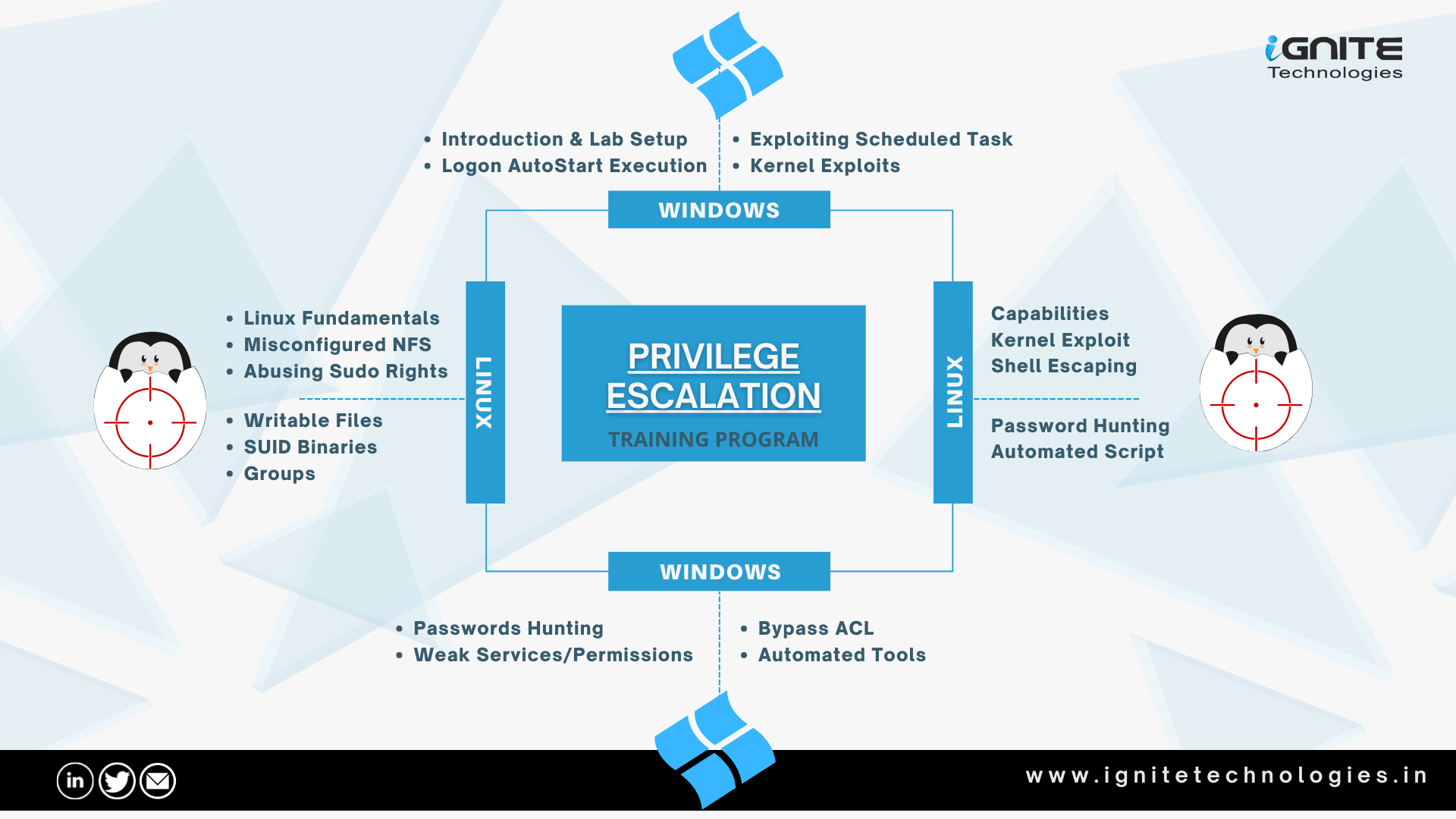
GitHub - Ignitetechnologies/Linux-Privilege-Escalation: This cheatsheet is aimed at the OSCP aspirants to help them understand the various methods of Escalating Privilege on Linux based Machines and CTFs with examples.




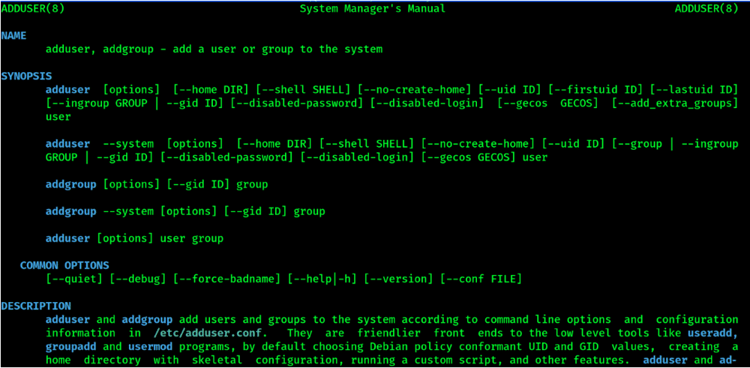

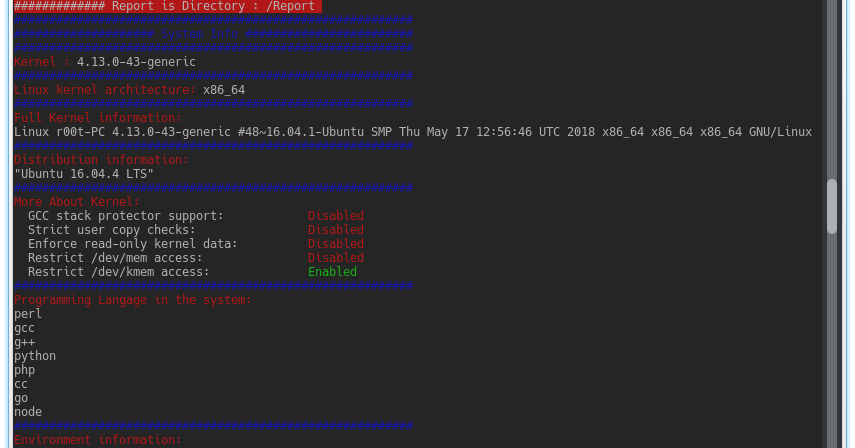







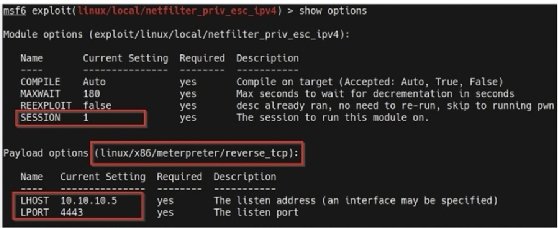
![Linux privilege checker - Advanced Infrastructure Penetration Testing [Book] Linux privilege checker - Advanced Infrastructure Penetration Testing [Book]](https://www.oreilly.com/api/v2/epubs/9781788624480/files/assets/0f21b2d6-ffb5-4181-b736-fc9d36a554da.png)